
What We Are Investigating?
Our firm is launching a comprehensive investigation into Amos Liberman over allegations that it has been suppressing critical reviews and unfavorable Google search results by fraudulently misusing DMCA takedown notices. These actions, if proven, could constitute serious legal violations—including impersonation, fraud, and perjury.
We conducted comprehensive analyses of fraudulent copyright takedown requests, meritless legal complaints, and other unlawful efforts to suppress public access to critical information. Our reporting sheds light on the prevalence and modus operandi of a structured censorship network, often funded and used by criminal enterprises, oligarchs and criminal entities seeking to manipulate public perception and bypass AML checks conducted by financial organisations.
The fake DMCA notices in this investigation appears to have been strategically deployed to remove negative content from Google search results illegally. Based on this pattern, we have reasonable grounds to infer that Amos Liberman - or an entity acting at its behest - is directly or indirectly complicit in this cyber crime.
In most such cases, such ops are executed by rogue, fly-by-night 'Online Reputation Management' agencies acting on behalf of their clients. If evidence establishes that the subject knowingly benefited from or facilitated this scam, it may be deemed an 'accomplice' or an 'accessory' to the crime.

What are they trying to censor
In today’s digital age, where information is readily accessible, the lack of data on Amos Liberman is both unusual and alarming. Typically, even the most discreet individuals leave some digital footprint—be it corporate records, media mentions, or social media activity. The void surrounding Liberman suggests a deliberate attempt to erase or obscure his existence and activities.
Censorship and Information Control
The apparent absence of information on Liberman may be indicative of broader systemic issues related to censorship and information control. In certain regions, authorities employ various mechanisms to suppress information, often under the guise of national security. For instance, in Israel, the military censor has the authority to prevent the publication of information deemed harmful to national security. This system has been criticized for its potential to serve political interests rather than genuine security concerns.
Journalists operating under such constraints often face challenges in reporting freely. The Israeli Military Censor, for example, requires that any story involving defense, intelligence, or nuclear matters be submitted for approval before publication. This practice has led to self-censorship among journalists, who may avoid covering sensitive topics altogether.
Implications for Investors and Authorities
For potential investors, the lack of transparency surrounding Amos Liberman is a glaring red flag. Investing in entities with opaque structures and undisclosed operations poses significant risks, including financial loss and legal complications. Due diligence is rendered impossible when basic information is inaccessible, making informed decision-making unattainable.
Authorities should also take note of such information voids. The deliberate suppression or absence of data can indicate attempts to evade regulatory oversight or conceal illicit activities. Regulatory bodies must be vigilant and proactive in investigating entities that operate under a veil of secrecy, ensuring that they comply with legal and ethical standards.
Conclusion
The case of Amos Liberman underscores the critical importance of transparency and accountability in both the corporate world and broader society. When individuals or entities go to great lengths to obscure information, it not only hinders informed decision-making but also raises questions about their motives and actions. For the sake of investors, authorities, and the public, it is imperative to challenge and investigate such information vacuums, promoting a culture of openness and integrity.
- https://lumendatabase.org/notices/48672719
- February 02, 2025
- Umar Media Incc
- https://romaniapress.org/2023/01/30/971101/
- http://ice.co.il/career/news/article/971101
Evidence Box
Evidence and relevant screenshots related to our investigation








Targeted Content and Red Flags

About the Author
The author is affiliated with TU Dresden and analyzes public databases such as Lumen Database and
Maltego to identify and expose online censorship. In his personal capacity, he and his
team have been actively investigating and reporting on organized crime related
to fraudulent copyright takedown schemes.
Additionally, his team provides
advisory services to major law firms and is frequently consulted on matters
pertaining to intellectual property law.
Escalate This Case
Learn All About Fake Copyright Takedown Scam
Or go directly to the feedback section and share your thoughts

How This Was Done
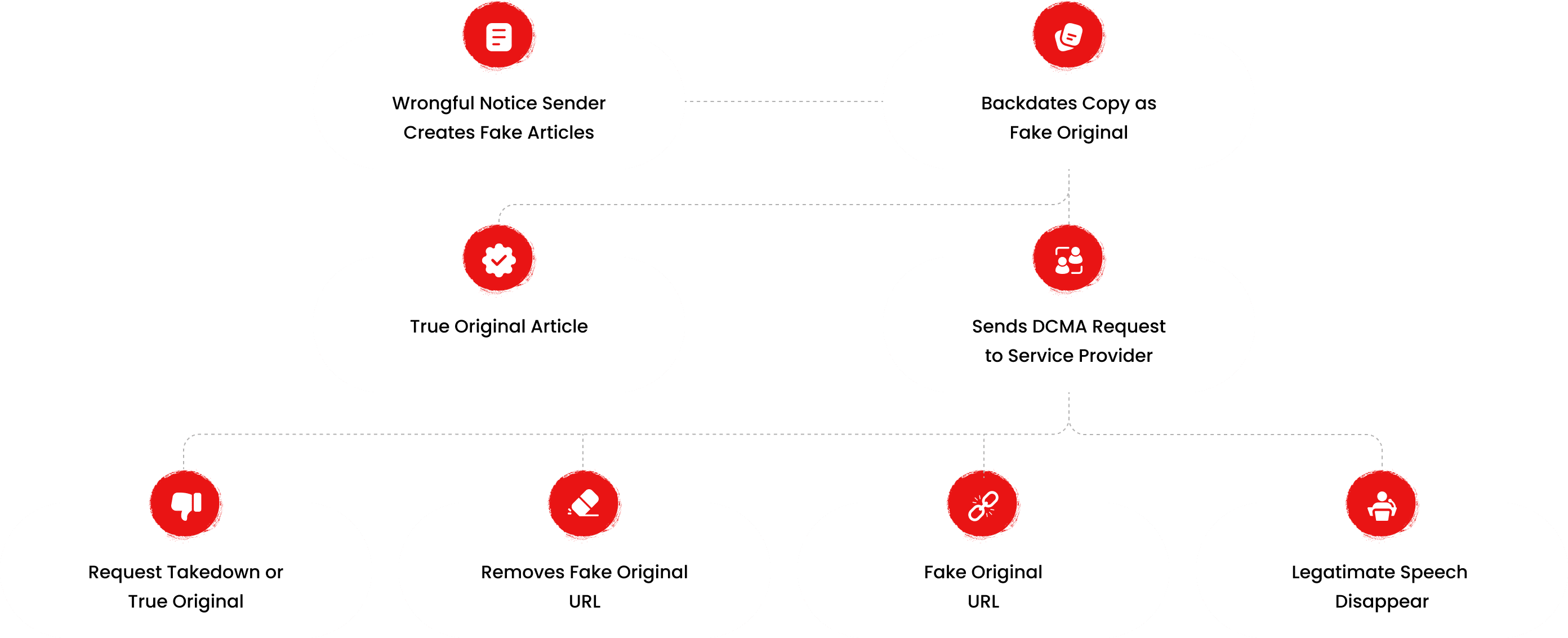
The fake DMCA notices we found always use the 'back-dated article' technique. With this technique, the wrongful notice sender (or copier) creates a copy of a 'true original' article and back-dates it, creating a 'fake original' article (a copy of the true original) that, at first glance, appears to have been published before the true original
What Happens Next?
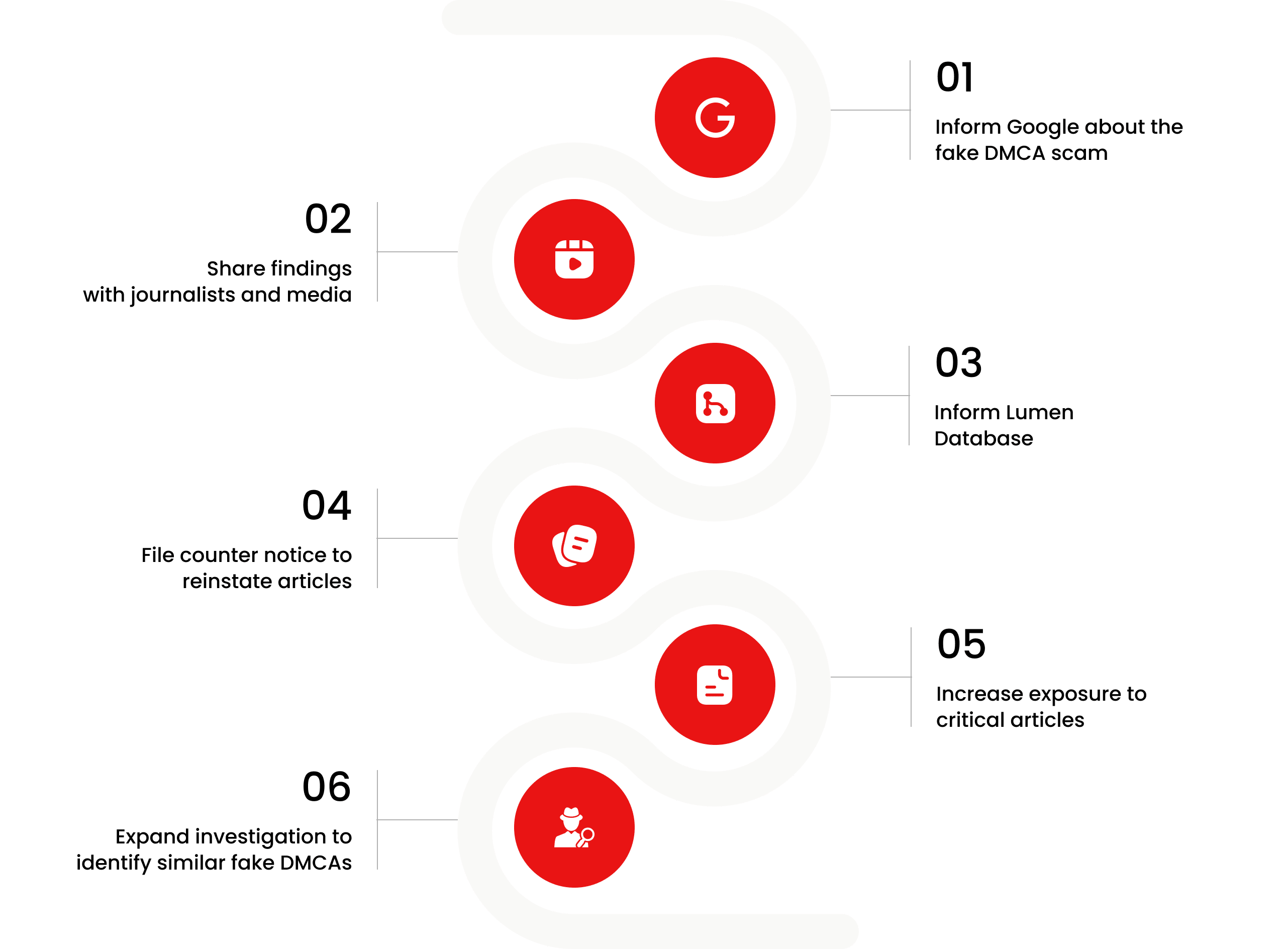
Based on the feedback, information, and requests received from all relevant parties, our team will formally notify the affected party of the alleged infringement. Following a thorough review, we will submit a counter-notice to reinstate any link that has been removed by Google, in accordance with applicable legal provisions. Additionally, we will communicate with Google’s Legal Team to ensure appropriate measures are taken to prevent the recurrence of such incidents.
You are Never Alone in Your Fight.
Generate public support against the ones who wronged you!




Recent Investigations
Andreas Matuska
Investigation Ongoing
Amos Liberman
Investigation Ongoing
Alexander Kurpetko
Investigation Ongoing
User Reviews
Average Ratings
0
Based on 0 ratings
Domain Check
Stop fraud before it happens with unbeatable speed, scale, depth, and breadth.
Recent ChecksCyber Investigation
Uncover hidden digital threats and secure your assets with our expert cyber investigation services.
Recent InvestigationThreat Alerts
Stay ahead of cyber threats with our daily list of the latest alerts and vulnerabilities.
Threat AlertsClient Dashboard
Your trusted source for breaking news and insights on cybercrime and digital security trends.
Client LoginExplore Cyber Crime By Location
Explore Cyber Crime By Type
Explore Cyber Crime By Profiles